Ledger wallets are among the most trusted hardware wallets for cryptocurrency enthusiasts. They provide an offline storage solution that keeps your private keys secure while allowing you to manage multiple cryptocurrency accounts. Logging in to your Ledger wallet is a critical step to ensure secure access to your funds. This guide will cover every aspect of Ledger login, including setup, security, troubleshooting, and best practices.
Ledger devices, such as Ledger Nano S and Ledger Nano X, provide a secure environment for cryptocurrency management. The login process ensures that only authorized users can access the wallet while protecting against phishing and hacking attempts.
Ledger login is the process by which a user gains access to their Ledger wallet using the Ledger Live application and the hardware device. Unlike software wallets, Ledger keeps private keys offline, which means even if your computer is compromised, your assets remain protected. Ledger login combines PIN authentication, optional passphrases, and device verification for maximum security.
Ledger login provides robust security through multiple layers:
Every Ledger device requires a PIN to unlock. Entering the PIN directly on the device ensures that malware or keyloggers on the computer cannot capture it. Without the correct PIN, unauthorized users cannot access your wallet.
Ledger generates a 24-word recovery phrase during setup. This phrase allows you to restore your wallet if the device is lost, stolen, or damaged. It is important to store the recovery phrase offline in a secure location.
Users can create an optional passphrase for added security. This enables hidden wallets, so even if someone has your Ledger device and PIN, they cannot access these accounts without the passphrase.
Ledger devices verify firmware authenticity during login. If unauthorized firmware is detected, access is blocked, ensuring your private keys remain safe.
Always begin at Ledger.com/start to download Ledger Live and follow official instructions. Avoid phishing websites to prevent fraud.
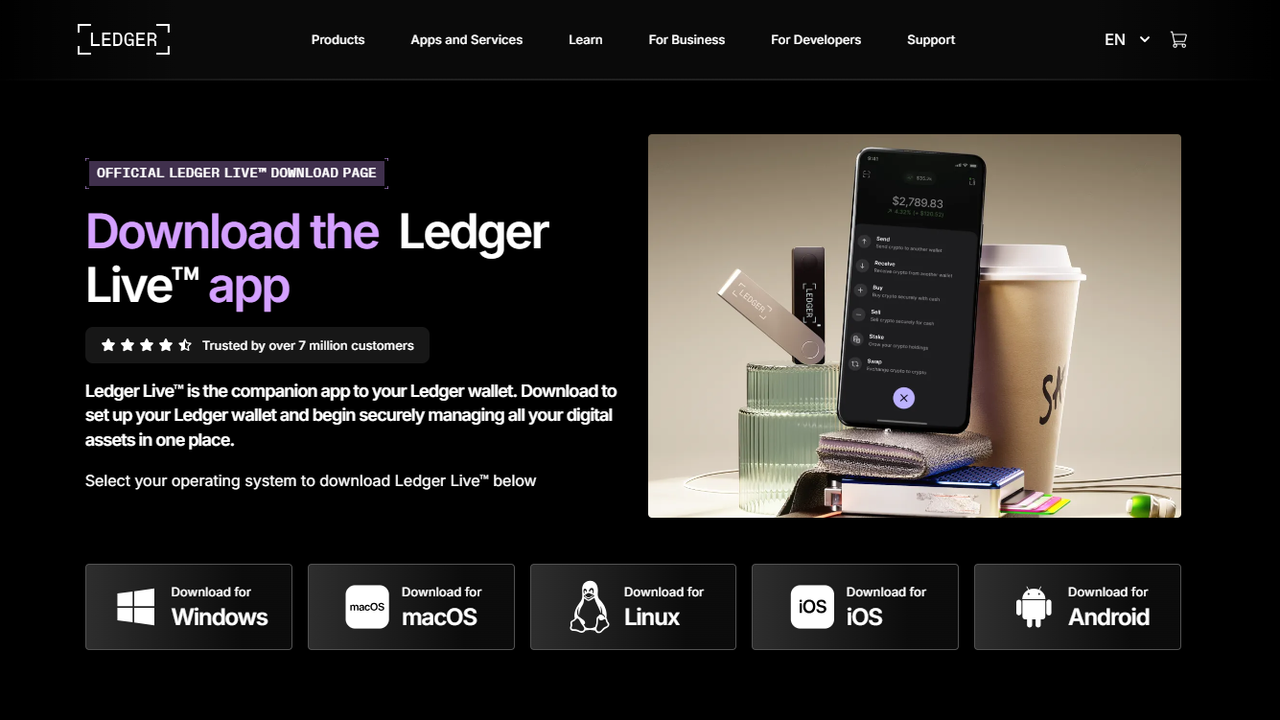
Ledger Live is the official software for managing Ledger wallets. It enables account management, cryptocurrency transactions, and firmware updates. Ledger Live is compatible with Windows, macOS, Linux, and mobile devices.
Connect your Ledger Nano S or Nano X to your computer via USB. Ledger Live will detect the device and guide you through the login process. Always use trusted computers to minimize security risks.
Your Ledger device will prompt for a PIN. Enter it directly on the device to authenticate securely.
If you have enabled a passphrase, you will be prompted to enter it during login. Passphrases provide access to hidden wallets for enhanced privacy.
Once authenticated, you can access your wallet in Ledger Live to manage balances, send and receive funds, and monitor accounts securely. Transactions require device verification to ensure private keys remain offline.
Ledger wallets support multiple cryptocurrencies, allowing you to manage accounts efficiently:
Always verify addresses directly on the device to prevent phishing attacks.
If your Ledger device is lost, stolen, or reset, you can restore access using your 24-word recovery phrase:
Hidden wallets created with passphrases offer an additional layer of privacy and security. These wallets are only accessible with the correct passphrase.
All transactions are signed offline on the Ledger device, keeping private keys safe from online attacks.
Ledger devices are designed to show signs of tampering. Always inspect your device before login.
Reset your device and restore the wallet using the recovery phrase. Never share your recovery phrase online.
Ensure Ledger Live is updated to the latest version compatible with your system.
Always verify transaction details on the Ledger device before confirming.
Ledger login is a vital step to ensure the security and management of your cryptocurrency assets. By following official instructions, using Ledger Live, and implementing best security practices, you can protect your funds from phishing attacks, malware, and unauthorized access.
Ledger combines offline private key storage, PIN protection, recovery phrases, passphrases, and device verification to provide a highly secure environment. Following this guide ensures safe, efficient, and confident management of your crypto portfolio.